Mobile devices store an increasing amount of sensitive information. As a result, they have become prime targets for sophisticated cyberattacks, which can lead to data leaks and financial losses. Devices with outdated operating systems are particularly vulnerable, as ready-made exploit kits can gain full system access with little to no user interaction.
In 2025, Ukrainians faced a wave of advanced iPhone attacks — initially through a tool called Coruna, and later via the more sophisticated DarkSword. Both exploit kits allow device compromise without any user interaction — simply visiting a website is enough.
An entire ecosystem stands behind these attacks: stolen Western cyber tools, Russian brokers, and targeted deployment against Ukrainian users. Below, we explain how this scheme works and why it became possible.
The Beginning: Treason, Greed, and Russian Connection
This story begins with the court verdict against Peter Williams, a former top manager at the company Trenchant. Having access to classified developments, Williams stole exploits — specialized hacking tools intended exclusively for the U.S. government and its closest allies — over a period of three years. Instead, he sold them to a Russian broker via encrypted communication channels in exchange for cryptocurrency.
These technologies ended up in the hands of Operation Zero, a company based in Saint Petersburg, which later resold them. According to the U.S. Treasury Department, this network has been purchasing tools for exploiting popular software and messengers since 2021.
Coruna: The First Wave of Attacks
On March 3, 2026, researchers from the Google Threat Intelligence Group (GTI) and iVerify exposed the active use of a full exploit chain, which they dubbed Coruna.
“The core technical value of this exploit kit lies in its comprehensive collection of iOS exploits, with the most advanced ones using non-public exploitation techniques and mitigation bypasses.” GTI writes.
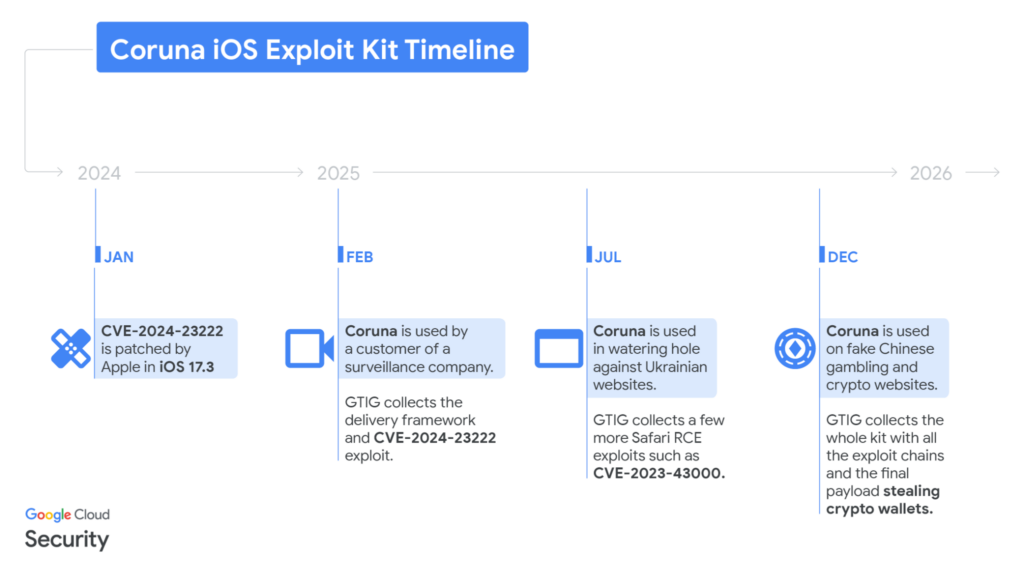
For Ukrainians, Coruna became a real threat in the summer of 2025. The group UNC6353 (linked to Russian intelligence services) hacked popular Ukrainian websites — from news resources to online stores — and embedded hidden malicious elements. Simply visiting the website resulted in a stealthy compromise and the subsequent exfiltration of sensitive data.
DarkSword: The Next Stage
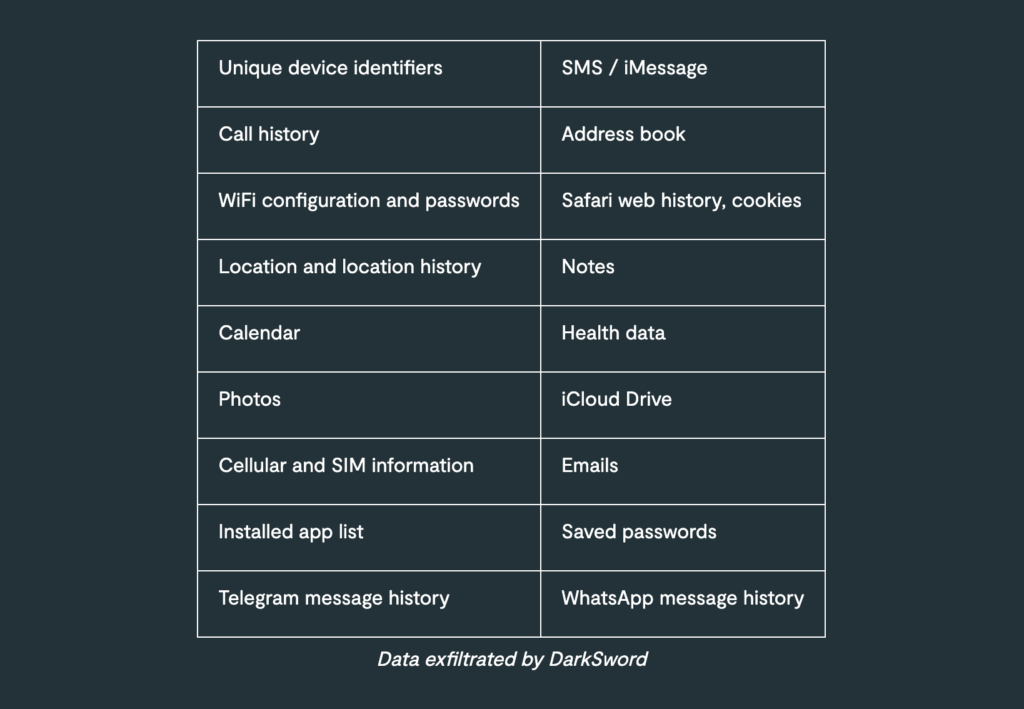
However, the attacks didn’t stop with Coruna. Recently, Lookout researchers discovered its successor — DarkSword. This is an even more advanced exploit chain targeting newer iOS versions (18.4 – 18.6.2, with some modifications supporting 18.7). Once infected, the exploit steals large volumes of data within seconds or minutes and instantly removes traces of its presence.
As iVerify notes, DarkSword uses a fileless execution model, meaning no traditional malware executable files are written to disk. Instead, it operates in memory, leveraging existing system processes. This approach significantly complicates detection, as most traces disappear after a device reboot — making it particularly effective for large-scale or semi-targeted attacks where speed and scale are more important than long-term persistence.
DarkSword specifically targets Ukrainian users. Researchers identified its malicious code on legitimate Ukrainian websites such as novosti.dn[.]ua and 7aac.gov[.]ua. This means attackers compromised existing websites to improve the delivery success rate and bypass trust barriers.
What Can DarkSword Steal?
After a compromise, attackers gain access to a broad range of sensitive data, including messages, contacts, photos, call history, app data, and potentially iCloud content. In practice, this means near-complete device access:
- Message history in Telegram and WhatsApp;
- Passwords, photos, contacts, and notes;
- Location data, calls, and SMS;
- Access to iCloud, etc.
Lookout researchers note that the emergence of DarkSword as a second iOS exploit chain signals a disturbing trend: a rapid growth of the black market for sophisticated exploits, where they are traded with little to no oversight. This allows buyers to repurpose such tools into custom malware, often leveraging AI to accelerate the process.
Who Is at Risk?
According to iVerify, the attack was not fully mass-market, but it was consistently triggered for users with Ukrainian IP addresses. Scripts could restrict execution based on geolocation, language, or other device characteristics. This suggests a hybrid model — selective targeting combined with mass delivery channels.
DarkSword exploits vulnerabilities in iOS versions 18.4 to 18.6.2 (released between March 31 and September 15, 2025), which are still widely in use, placing a large number of iOS users at risk.
Older models such as iPhone XS, XR, X, 8, 7, or earlier are especially vulnerable, as they do not support the latest updates. In these cases, upgrading to a supported device is the only robust defense.
However, newer iOS devices are also at risk if they are not updated in a timely manner. As of March 25, 2026, the latest iOS version is 26.4.
Researchers also found that Coruna and DarkSword do not work in Lockdown Mode, as this feature blocks many of the attack vectors these exploits rely on.
Basic Protection: How to Stay Safe
- Always update iOS/iPadOS to the latest version. Apple developers constantly patch the vulnerabilities used by Coruna and DarkSword.
- Enable Lockdown Mode. (Instructions on how to enable and manage Lockdown Mode are typically provided by Apple).
- Disable Link Previews. This applies to all messengers and email to prevent the automatic loading of malicious code.
- Regularly reboot your device. Since many modern viruses “live” only in RAM, a reboot can interrupt the operation of a malicious process.
How to Protect Your Website (Minimal Checklist):
- Qualified Technical Support: Ensure someone is responsible for infrastructure security, e.g., website administrator.
- Backups: While they don’t protect against a hack, they prevent data loss. Regularly check backup integrity.
- Updates: Keep the OS, CMS, and plugins up to date — many attacks exploit vulnerabilities already fixed in newer versions.
- Unique Account Policy: Avoid shared access to maintain accountability and track changes
- Admin Login Protection: Enable Two-Factor Authentication (2FA) and CAPTCHA.
- Principle of Least Privilege: Assign roles strictly, limiting Admin access while granting Editor privileges to all other personnel.
- Offboarding: Conduct regular access reviews and revoke permissions for those who no longer require them.
- Additional Measures: Enforce HTTPS, use DDoS protection, configure a WAF (Web Application Firewall), and implement real-time monitoring of critical events.