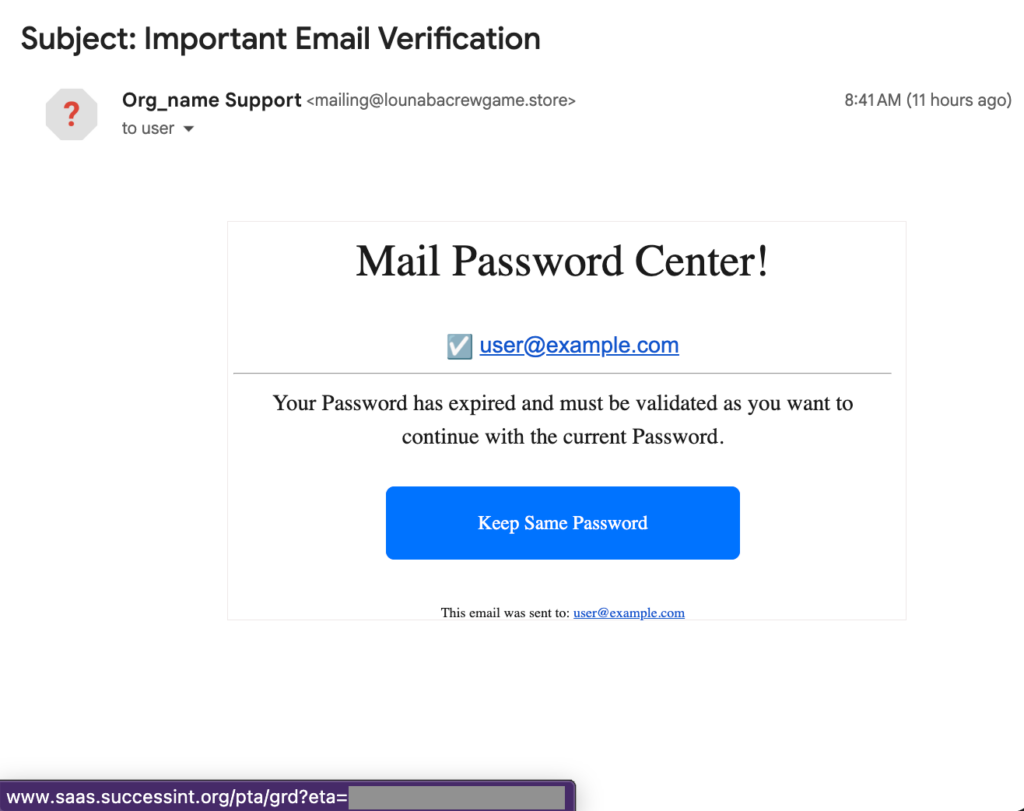
We have received a phishing message for analysis. The message follows a common social engineering pattern – it warns the recipient that their password is about to expire and urges them to change it via a link. While the email itself appears relatively typical, the phishing infrastructure behind the link reveals a scalable credential harvesting mechanism.
The phishing URL contains a unique identifier – the recipient’s email address. Once the link is opened, the phishing page extracts the domain from the email and dynamically adapts its interface to impersonate the corresponding organization. The page loads the legitimate website in the background, retrieves the domain’s favicon, and presents a generic login form designed to appear associated with the target organization.
Captured credentials and additional victim metadata are sent to an external backend server. After the submission process, the victim is redirected to the legitimate website associated with the extracted domain, which helps conceal the phishing attempt.
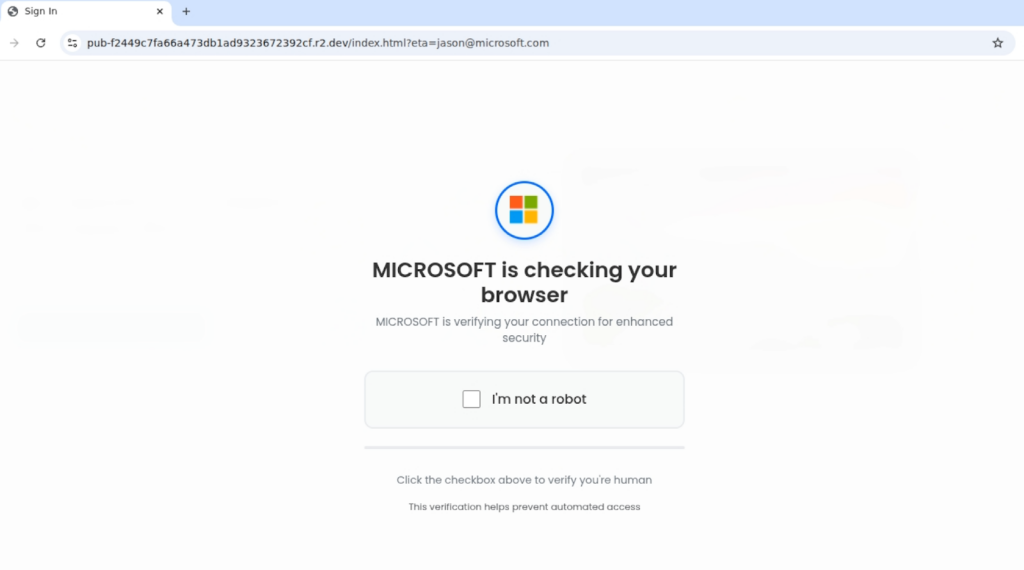
For demonstration purposes, this report illustrates the workflow using a Microsoft domain, but the phishing kit is domain-agnostic and automatically adapts to any organization based on the email address embedded in the phishing link. Similar phishing attempts were also observed targeting representatives of Ukrainian civil society organizations.
Initial access and redirect chain
The victim is first directed to an intermediate URL:
A redirect chain then occurs:

r2[.]dev – phishing page hosted on Cloudflare R2 (R2 allows for free hosting of static assets without egress fees).
Before displaying the login form, the page shows a fake anti-bot verification screen with a checkbox labeled “I’m not a robot” and a progress indicator. This is purely social engineering and does not involve any real CAPTCHA.
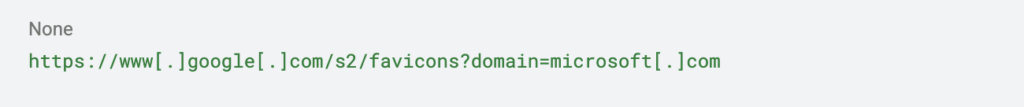
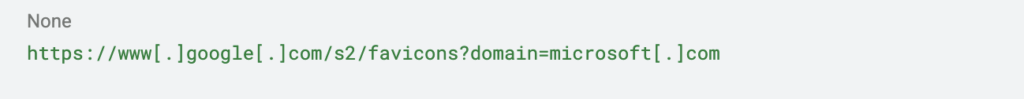
During the “verification”, the page:
- displays the victim’s brand name
- retrieves the favicon using the Google favicon service
- loads the legitimate website in a background iframe
The phishing page accepts the parameter ‘eta’, which contains the victim’s email address. The page automatically inserts this email into the login form and extracts the domain. The interface is then dynamically customized based on that domain.
The attackers do not simply imitate the visual design. Instead, they load the real website of the target organization as a blurred background to reinforce the perception that the victim is logging into the legitimate org’s website.
Credential harvesting process
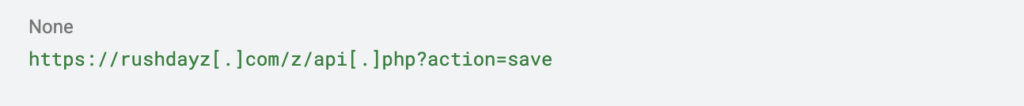
When the victim enters a password, the page collects and sends not only the credentials but also additional metadata about the victim. Traffic analysis shows a POST request to:
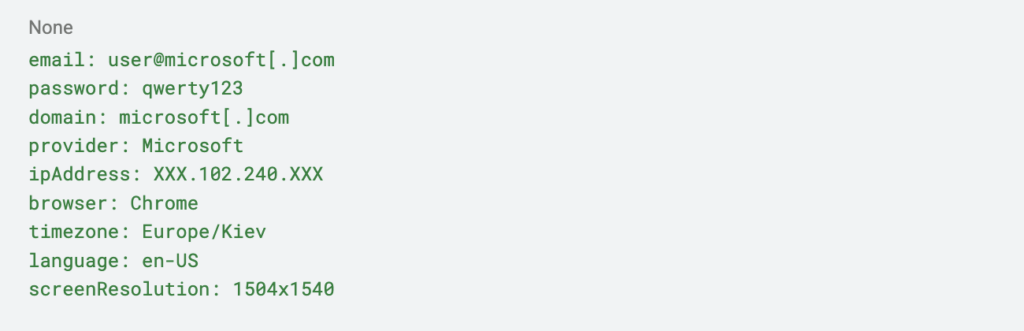
The captured submission contained the following values:
The server responded with:
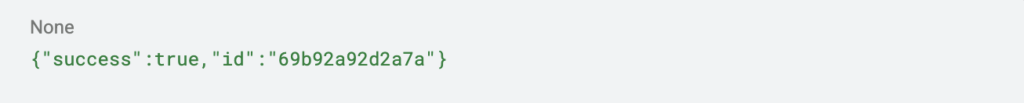
This confirms that the backend successfully received and stored the harvested credentials.
Attacker tactics
Several common phishing techniques are implemented in this kit.
- Victim pre-profiling. The email address is embedded directly in the URL (eta parameter), allowing the phishing page to personalize the interface automatically.
- Dynamic branding based on the victim’s domain. This means the kit can be reused against many organizations without rewriting the code.
- The legitimate website of the victim organization is loaded as a background iframe. This increases the perceived legitimacy of the login prompt.
- A staged “invalid password” scenario. After the first credential submission, the page displays the message: “Invalid password. Please try again.” The password field is cleared, and the victim is prompted to re-enter the password. This tactic allows attackers to verify that the victim did not accidentally mistype the password and collect multiple credential samples.

After the second attempt, the page resets the local counter ‘loginAttempts’ and redirects the victim to the legitimate website. This helps conceal the attack, as the victim may assume that the login simply failed and that they were redirected back to the normal website.
This is not a single static phishing page impersonating a special org but a reusable phishing kit that automatically customizes its appearance based on the victim’s domain extracted from the email parameter. Only the eta value changes, while the interface and logic adapt automatically.
This significantly increases the scalability of the campaign and makes it suitable for targeting multiple organizations with minimal configuration.
IOCs:
Domains:
www[.]saas[.]successint[.]org
pub-f2449c7fa66a473db1ad9323672392cf[.]r2[.]dev
rushdayz[.]com
URL paths:
/pta/grd
/index.html?eta=
/z/api.php?action=save